Multi-factor Authentication (MFA) and Conditional Entry (CA) insurance policies are highly effective instruments to guard Azure AD customers’ identities.
As an example, one could enable entry solely from compliant units and require MFA from all customers.
Nevertheless, due to Azure AD authentication platform structure, customers can bypass residence tenant MFA and CA insurance policies when logging in on to useful resource tenants.
This weblog submit tries to shed some mild on how Azure AD authentication works under-the-hood.
We’ll introduce the difficulty, describe the right way to exploit it, present the right way to detect exploitation, and at last, the right way to forestall the exploitation.
The weblog is co-authored with @SravanAkkaram and relies on his findings.
This story, like many others, started after a tweet:
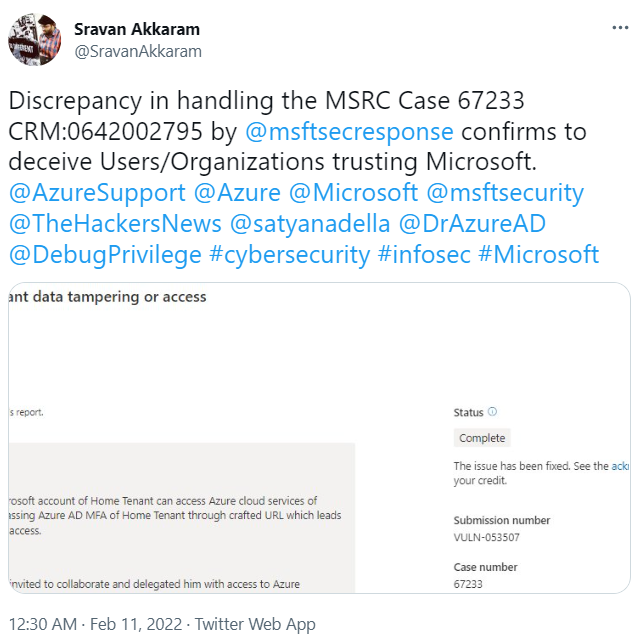
I replied to Sravan and requested him to DM me if he’d like me to take a look on his case. Fortunately, he did ?
Azure Lively Listing (Azure AD) is Microsoft’s Identification and Entry Administration (IAM) service utilized by Microsoft 365 and Azure, but additionally by hundreds of third get together service suppliers.
An occasion of Azure AD known as tenant.
Dwelling and useful resource tenants
Customers can log in to the tenant utilizing the authentication strategies configured by the directors. Microsoft is looking this to residence tenant.
Customers are additionally in a position to log in to different tenants, if they’re invited there as visitors. Microsoft calls these tenants useful resource tenants.
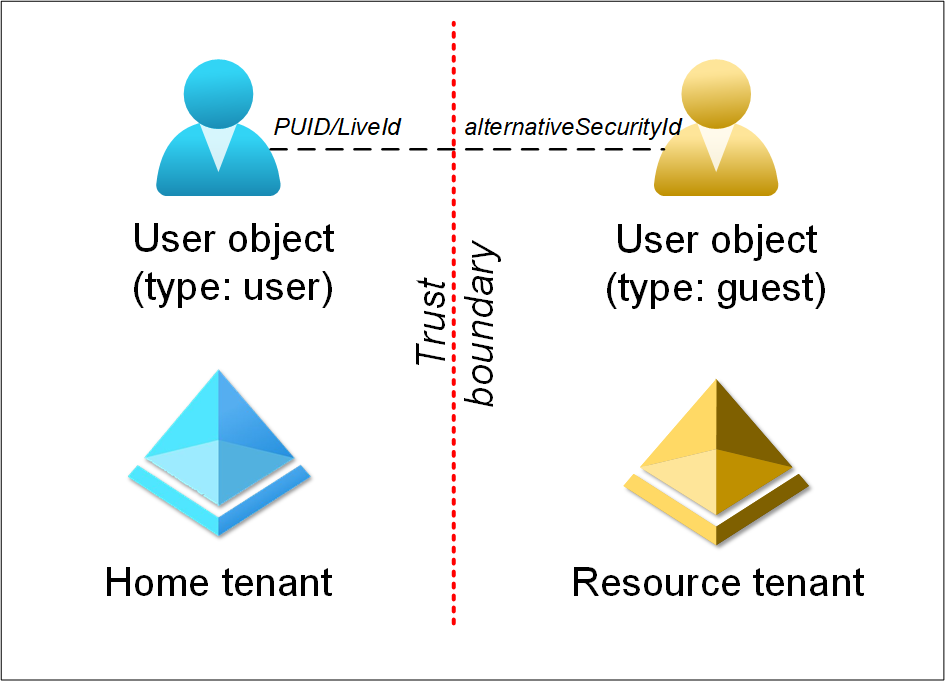
After person accepts the invitation, a corresponding person object is created to the useful resource tenant.
The 2 objects are linked to one another. The useful resource tenant person object has an array of alternativeSecurityIds and one in every of them (of kind 5) equals the PUID (aka LiveId) attribute of the house tenant person object.
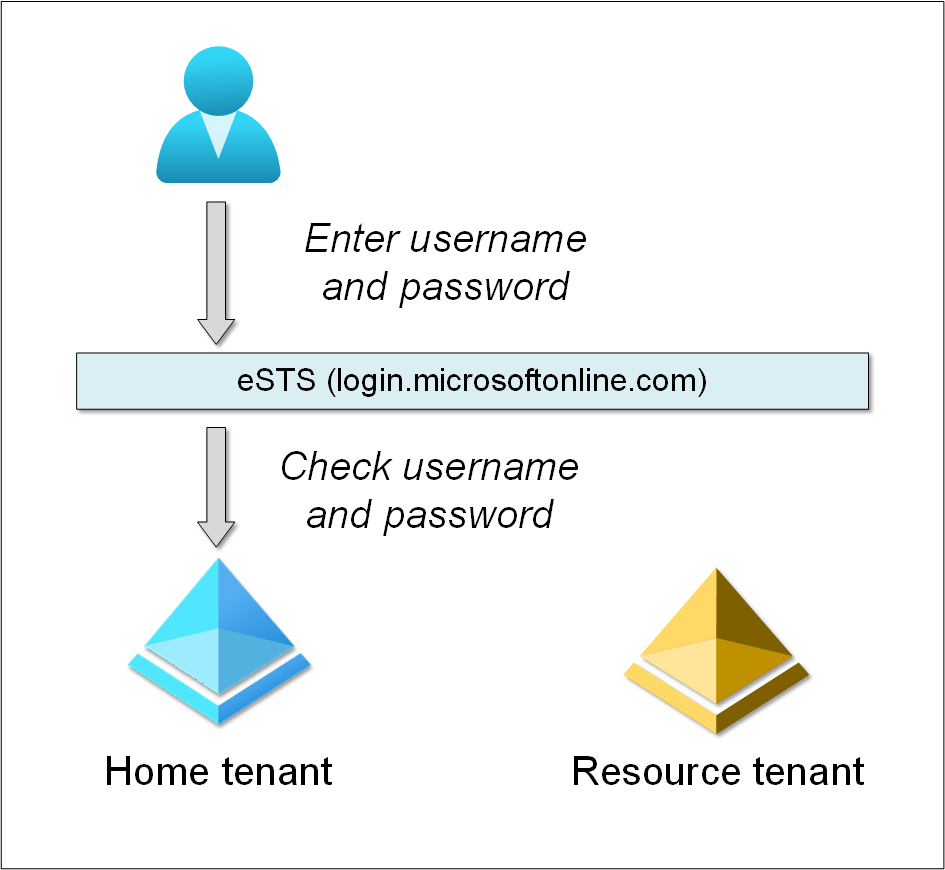
eSTS
Primarily based on our observations, when logging in to Azure AD tenant, you might be truly logging in to eSTS. However what’s eSTS?
In response to Microsoft Azure SOC 3 Report. October 1, 2017 – September 30, 2018:
Developed Safety Token Service (eSTS): eSTS offers a stateless service that accesses a number of principal and key shops.
eSTS absorbs the roles of a number of STSs, in order that customers see one Azure AD STS.
eSTS depends on MSODS to carry info required to finish the authentication.
eSTS helps quite a lot of protocols together with OAuth 2.0, Open ID Join, WS-Fed, and Safety Assertion Markup Language (SAML) protocol.MSODS: MSODS is Microsoft On-line Listing Providers, a characteristic of Azure Lively Listing that additionally consists of Azure Lively Listing B2B.
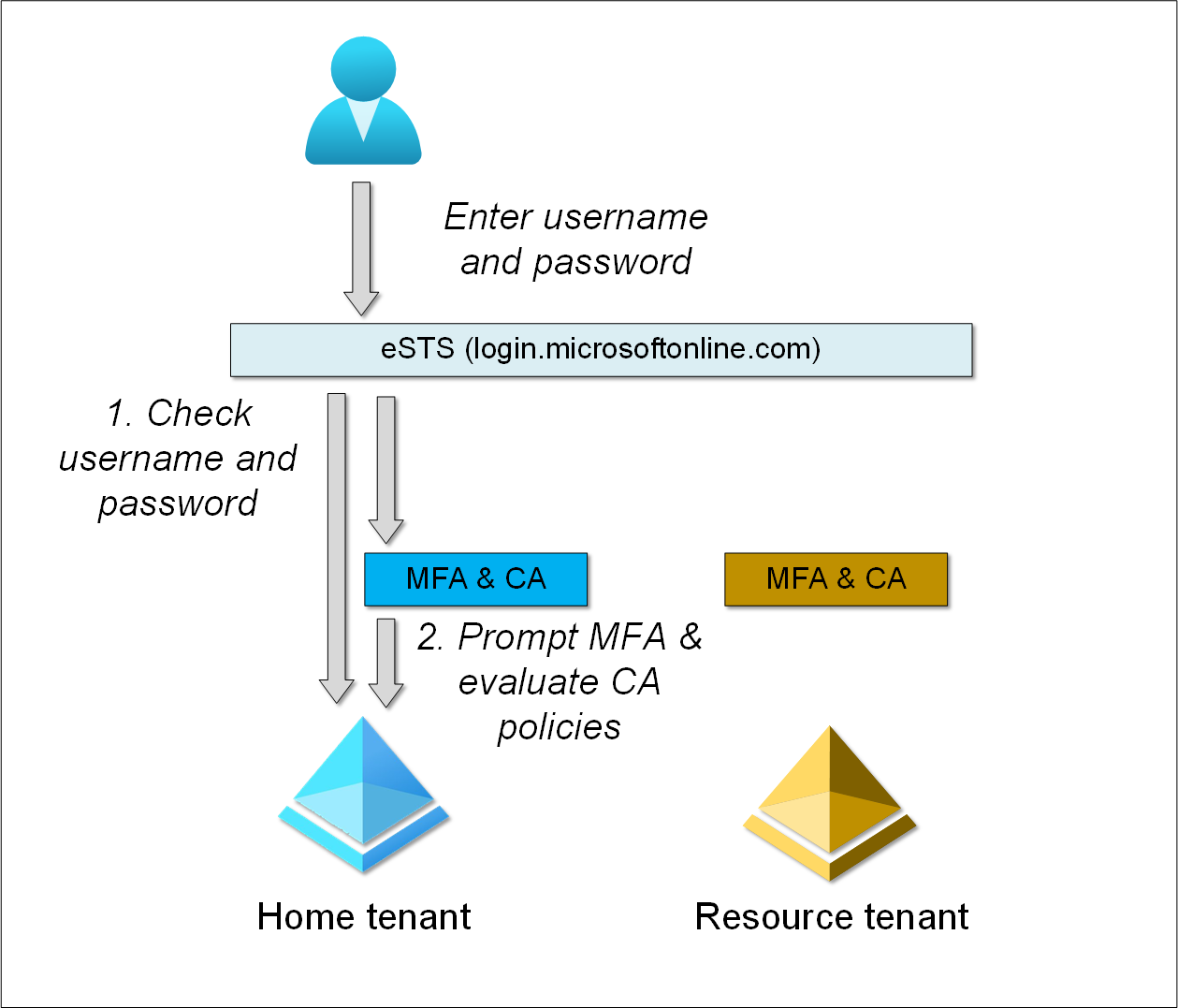
Right here is an instance of a tenant utilizing username and password. Consumer goes to login.microsoftonline.com and offers username and password.
eSTS then checks the offered credentials towards residence tenant Azure AD.
Multi-factor authentication (MFA) and Conditional Entry (CA)
MFA could be utilized both per person, with Safety Defaults, or utilizing Conditional Entry (requires Azure AD Premium).
With Conditional Entry one can
grant or block entry to companies primarily based on the person, system, utility, person’s location, and so forth.
Each MFA and CA are utilized post-authentication, i.e., after logging in to eSTS.
Furthermore, MFA and CA are configured per tenant.
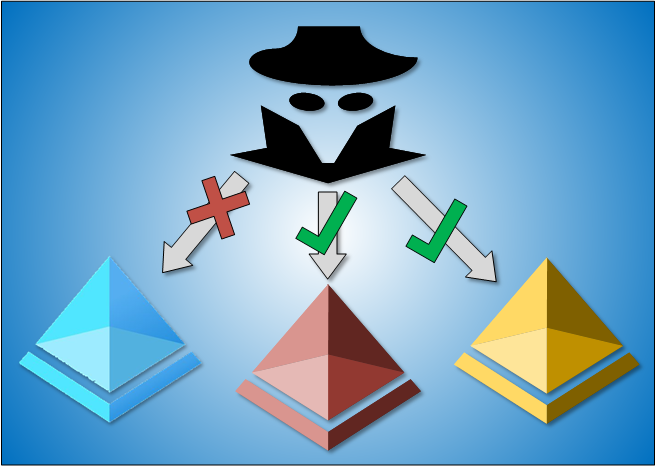
Right here is an instance, the place person is logging in to residence tenant (login.microsoftonline.com):
- eSTS checks the offered credentials towards person’s residence tenant.
- Dwelling tenant MFA is prompted and CA insurance policies evaluated.
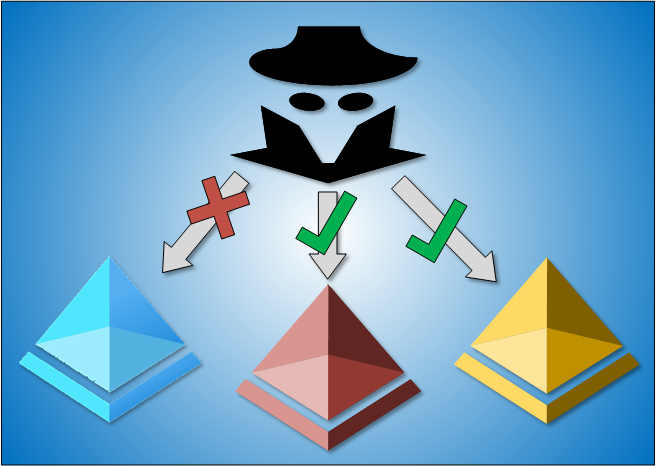
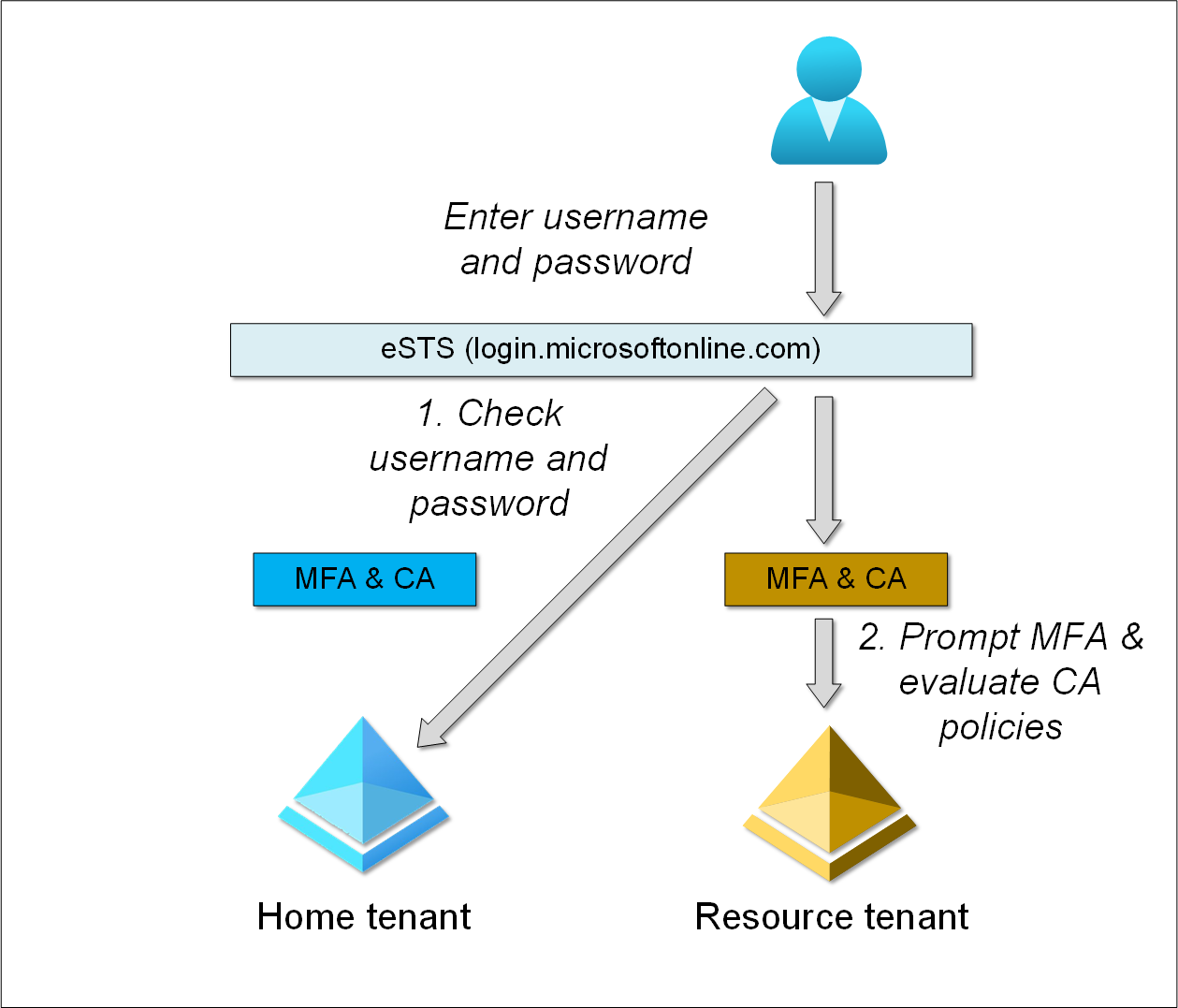
Sravan discovered that when logging in on to useful resource tenant, residence tenant MFA and CA should not utilized.
Right here is an instance, the place person is logging on to useful resource tenant (login.microsoftonline.com/<useful resource tenant area or id>):
- eSTS checks the offered credentials towards person’s residence tenant.
- Useful resource tenant MFA is prompted and CA insurance policies evaluated.
Word: If the use tries to entry residence tenant companies after logging in to useful resource tenant, residence tenant MFA and CA insurance policies are utilized usually.
This type of collaboration between two tenants known as B2B collaboration, and requires that the person is first invited to the useful resource tenant a visitor.
Relying on the useful resource tenant configuration, it could or could not have MFA and/or CA insurance policies configured. Utilizing
Sravan seen that there are some useful resource tenants which permits customers to log in with out invitation.
These tenants are utilizing Azure AD B2C service:
Azure AD B2C is a separate service from Azure Lively Listing (Azure AD). It’s constructed on the identical expertise as Azure AD however for a special function. It permits companies to construct buyer dealing with functions, after which enable anybody to enroll into these functions with no restrictions on person account.
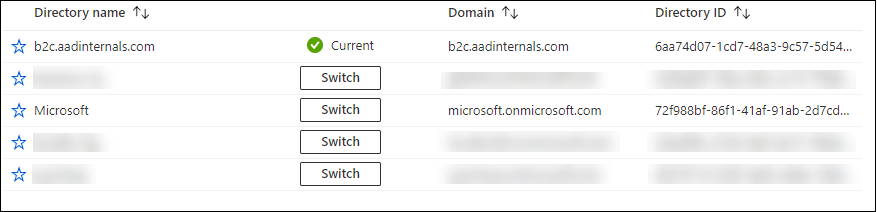
Many well-known shopper manufacturers are utilizing Azure AD B2C. As I didn’t need to listing these tenants right here, I created one for demonstration functions: https://portal.azure.com/b2c.aadinternals.com
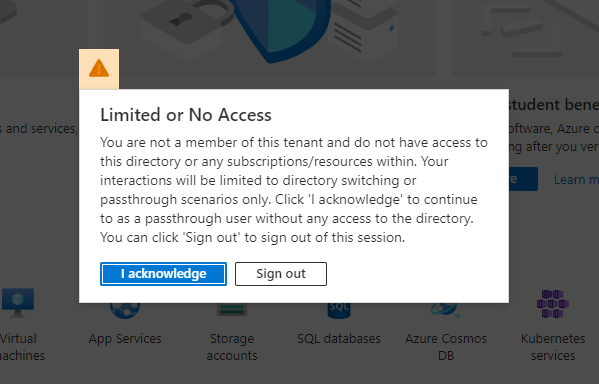
You’ll be able to log in to the tenant with out MFA, regardles of your house tenant settings. You’ll be given the next error:
After clicking I acknowledge, you possibly can pull down the person menu and choose Swap listing:
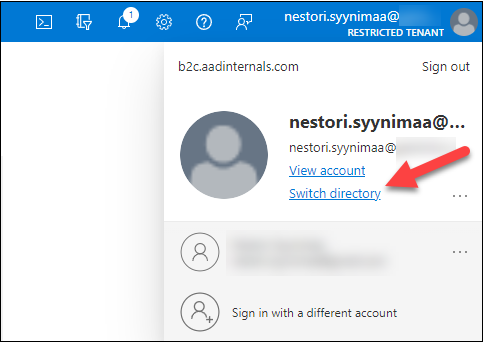
This lets you view all tenants you might be member of and change to them:
Bypassing MFA and CA
Let’s see how we are able to exploit the authentication move. First, we create a CA rule to dam entry for Nestor Wilke.
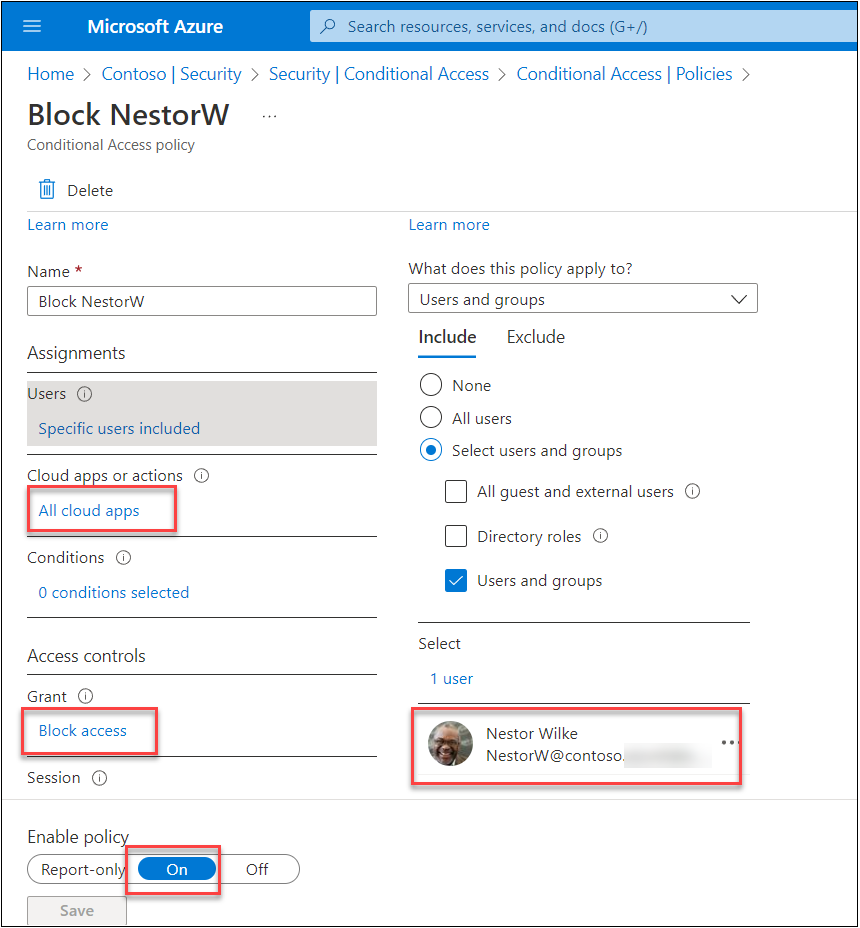
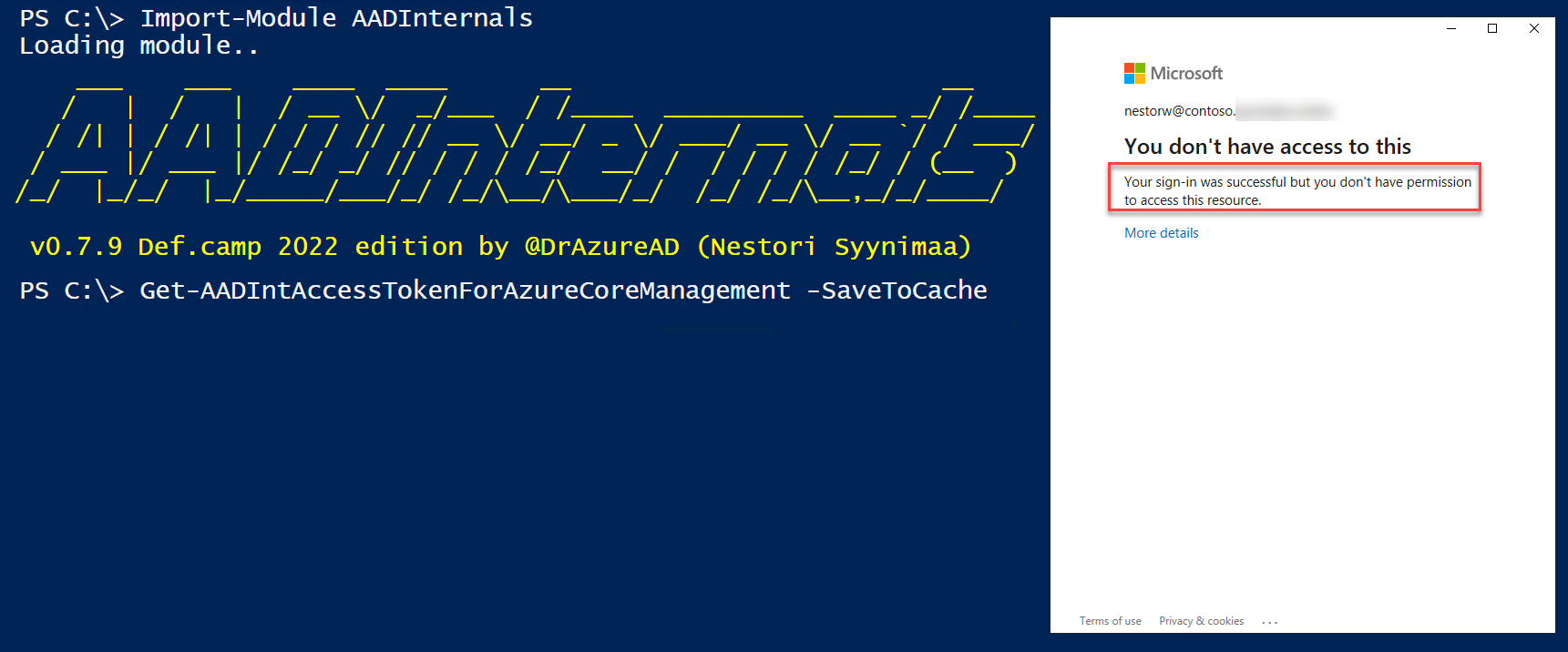
When making an attempt to get an entry token utilizing AADInternals, we are able to see that the sign-in was succesful however as a result of CA, you don’t have permission to entry this useful resource.
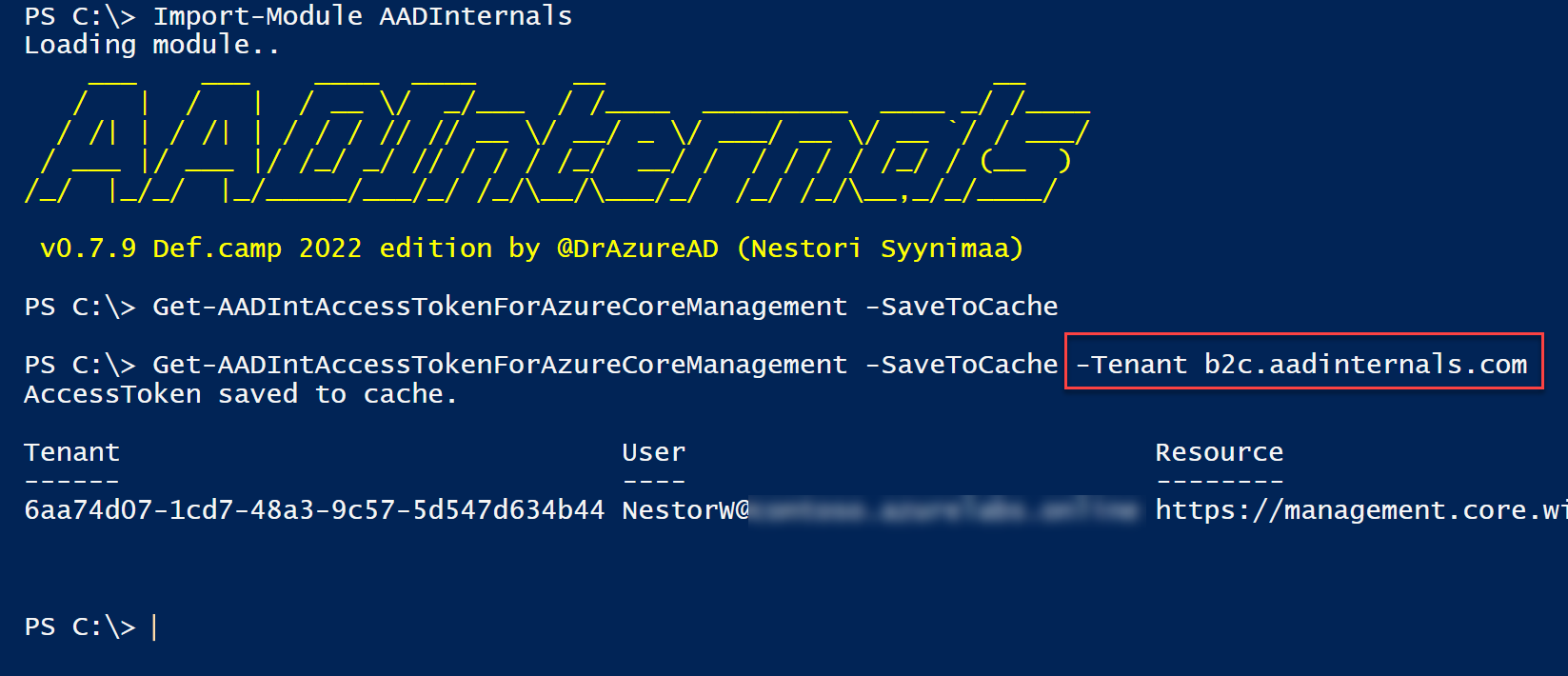
Nevertheless, if we offer b2c.aadinternals.com because the tenant, residence tenant CA will not be evaluated!
Word: Useful resource tenant MFA and CA are nonetheless utilized (if outlined).
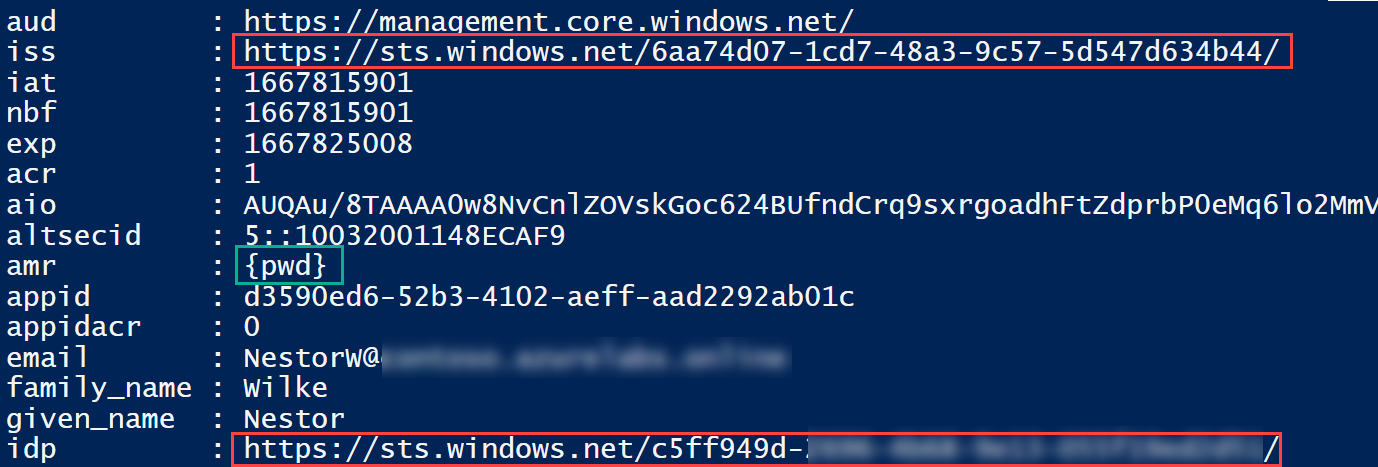
The returned entry token exhibits that the issuer (iss) declare and identification supplier (idp) claims are completely different.
We are able to additionally see that there isn’t any MFA included in authentication strategies (amr) declare.
Which means residence tenant directors can’t block entry to useful resource tenants utilizing Conditional Entry.
This isn’t very intuitive, as one would assume blocking entry to residence tenant would block entry to all tenants too.
Exploiting
So, how would risk actors exploit this? To start with, you’d must have person’s credentials.
When you have these, you possibly can log in to any useful resource tenant the person is member of, and do something the person has permission to do.
The most typical state of affairs can be to entry Groups.
However what for those who don’t know any useful resource tenants the person is member of? One other Sravan’s discovering will assistance on this. He seen that B2C tenants lets you log in, even whenever you’re not invited as visitor:
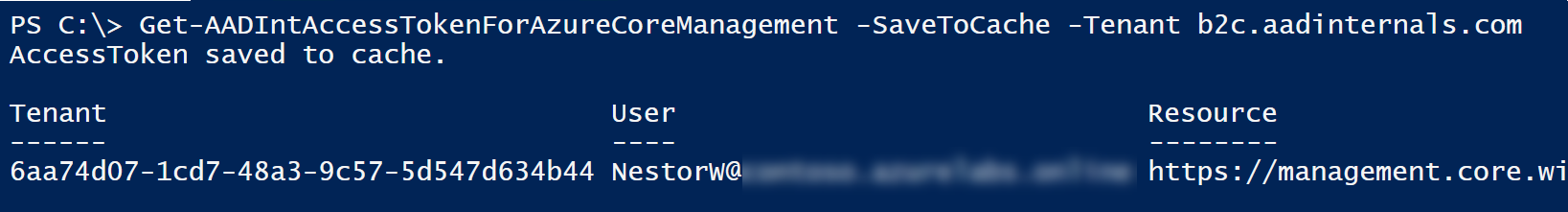
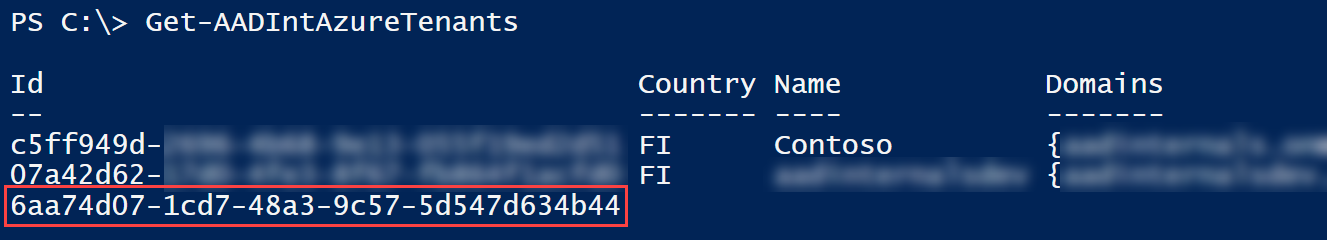
Now you need to use AADInternals to get listing of person’s tenants. The final tenant is the one we logged in, and doesn’t have another info in addition to the tenant id.
The remainder of the tenants are those the person can entry.
Log ins to useful resource tenants are additionally logged in sign-ins log. Right here we are able to see the occasions of the examples above:
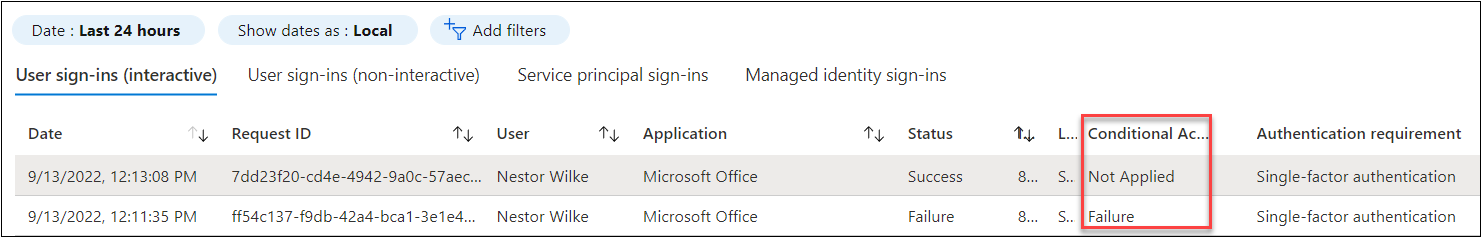
Particulars of the primary occasion exhibits the useful resource and residential tenant ids.
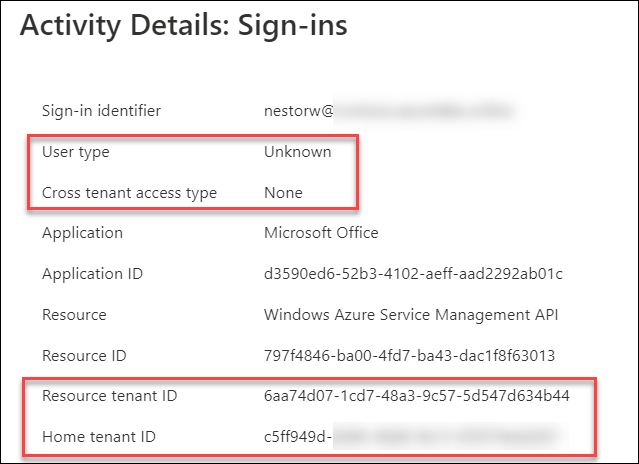
The Consumer kind and Crosstenant entry kind is dependent upon the useful resource tenant kind:
| Element | B2B | B2C |
|---|---|---|
| Consumer kind | Visitor | None |
| Cross tenant entry kind | B2B collaboration | Unknown |
Cross-tenant entry settings
Cross-tenant entry settings is approach to management each outbound and inbound collaboration.
Outbound settings are configured by residence tenant directors and inbound settings by useful resource tenants.
Word: Any tenant could be residence tenant, useful resource tenant, or each on the identical time.
With outbound settings, residence tenant directors can configure default settings to both block or enable entry to all useful resource tenants:
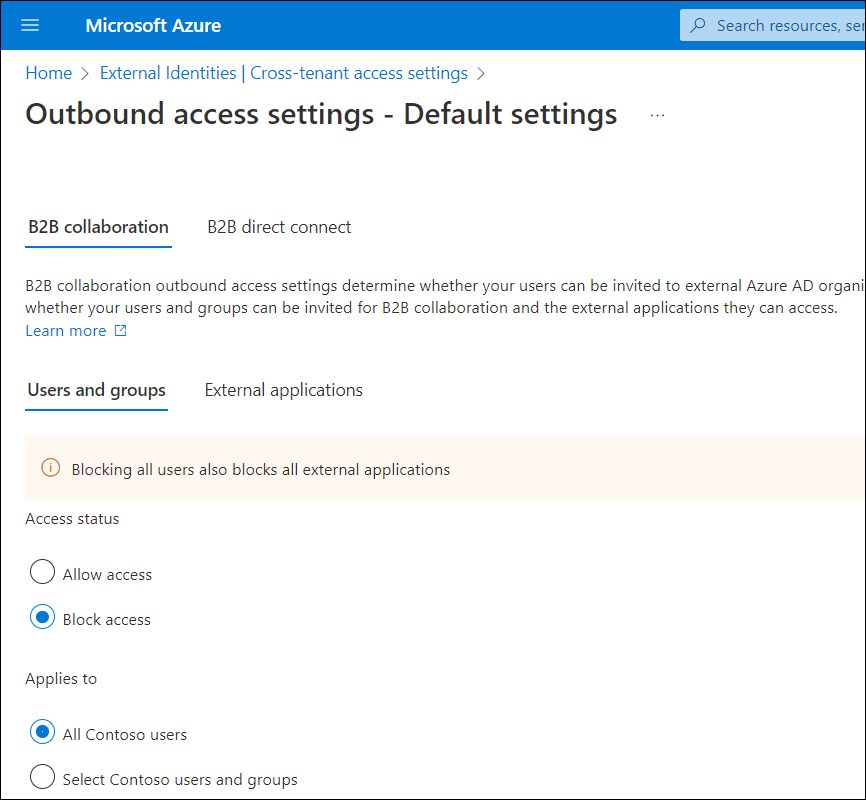
This works in an analogous method than the “Default Deny” and “Default Enable” guidelines in firewalls.
Dwelling tenant admins can even customise settings for every useful resource tenant:
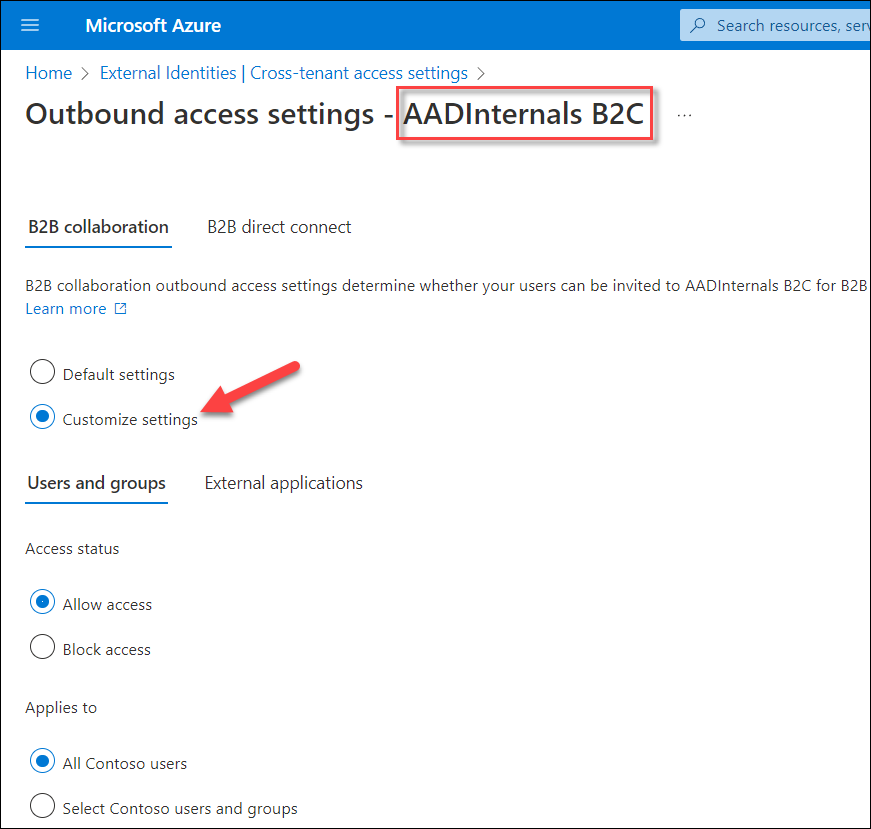
Which means residence tenant admins can block entry however can’t implement residence tenant MFA & CA to permit entry to useful resource tenants.
As a lot as I like this type of “default deny” entry settings, it will possibly have extreme penalties to business-critical functions as Microsoft additionally warns:
Altering the default inbound or outbound settings to Block entry might block present business-critical entry to apps in your group or accomplice organizations. You should definitely use the instruments described in Cross-tenant entry in Azure AD Exterior Identities and seek the advice of with what you are promoting stakeholders to determine the required entry.
Furthermore, blocking all exterior entry simply to be sure that customers (or adversaries) can’t bypass residence tenant MFA & CA sounds a bit overkill.
Correspondence
| Date | Case ID | Description |
|---|---|---|
| Jul 18th 2021 | 66317 | Unique submission “Bypass MFA & Cross-tenant knowledge tampering or entry” |
| Aug seventh 2021 | 66317 | Closed as “by-design” |
| Aug twenty seventh 2022 | 67233 | Resubmit with POC. “Bypass MFA / Cross-tenant knowledge tampering or entry” |
| Feb twenty first 2022 | 70402 | Separated from case 67233: “Azure administration API exposes person’s visitor and residential tenant no matter residence tenatns safety insurance policies” |
| Mar eleventh 2022 | 67233 | MFA half closed as “by-design”. Response: “The useful resource tenant is at all times chargeable for Azure AD Multi-Issue Authentication for customers, even when the visitor person’s group has Multi-Issue Authentication capabilities” Documentation up to date: |
| Jun seventeenth 2022 | 70238 | Cross-tenant entry (opened internally by MSRC, standing unknown).
Microsoft applied a Restricted or No Entry pop-up when signing in to Azure AD Portal of useful resource tenants the place the visitor person has restricted or no permissions: |
| Aug twenty second 2022 | 70402 | Closed as “by-design”. |
| Oct twenty seventh 2022 | * | Remaining response from MSRC |
Remaining response from Microsoft Safety Response Middle (MSRC):
As at all times, your wonderful analysis is at all times priceless to us for flagging potential issues. We took the time to fastidiously evaluation your discovering.
On this case, we’ve made a thought of determination to enable finish customers to see their listing of tenants within the tenant switching expertise unbiased of the person insurance policies of a specific tenant. The relevant tenant listing is a part of system metadata, and not topic to a selected tenant’s person insurance policies. The present method is vital for usability for tenant switching, which clients think about a vital characteristic.
Analysis of login for authorization of a visitor is completed on the useful resource tenant except clients select to leverage cross-tenant entry settings, which might enable delegation of analysis to the person’s residence tenant, however the useful resource tenant’s insurance policies are at all times utilized. Moreover, if an admin want to management the place their customers are in a position to entry and be a visitor person, they can leverage cross-tenant entry settings to dam outbound collaboration to restrict entry to solely permitted useful resource tenants.
Whereas the stability of person expertise and resource-dominant coverage has led us to the present design (which works as supposed), we do perceive your issues and can search for alternatives to boost the mannequin on this space.
Consumer’s residence tenant Conditional Entry (CA) insurance policies and MFA should not evaluated when the person is logging in on to the useful resource tenant.
As such, residence tenant directors do not need full management of the authentication move of their customers and to guard their tenant membership knowledge.
B2B useful resource tenant directors can implement residence tenant MFA & CA with useful resource tenant CA and cross-tenant settings. This isn’t potential for B2C useful resource tenants.
Nevertheless, residence tenant directors can block entry to all or particular useful resource tenants utilizing cross-tenant entry settings.
Abstract of the house tenant management choices
| Description | |
|---|---|
| ✅ | Enable or block entry to all useful resource tenants (default settings) |
| ✅ | Enable or block entry to particular useful resource tenants (customised settings) |
| ❌ | Implement residence tenant MFA & CA when accessing useful resource tenants |
Suggestions
We advocate directors to dam entry to all useful resource tenants (the place believable) and to permit entry to solely these useful resource tenants that implement residence tenant MFA and CA insurance policies.
We now have steered to Microsoft that residence tenant MFA & CA insurance policies ought to at all times be evaluated.
About Sravan Akkaram (@SravanAkkaram)

Sravan Akkaram is a tech fanatic, a safety researcher and a Blue Teamer by career. He works as a Senior Cyber Safety Analyst at Accenture. His core expertise embrace Incident Response, Malware Evaluation and risk looking. He’s additionally fascinated about studying how functions work to seek out bugs and vulnerabilities.












+ There are no comments
Add yours