
Directors can use groups insurance policies for controlling what customers can do in Microsoft Groups.
On this weblog, I’ll present that these insurance policies are utilized solely in consumer and thus could be simply bypassed.
Insurance policies are utilized in Microsoft Workplace 365 and Azure AD for securing entry to providers and knowledge. Moreover the frequent identification and system entry insurance policies,
Microsoft has supplied a set of Groups particular insurance policies:
- Groups and channel insurance policies
- Messaging insurance policies
- Assembly insurance policies
- App permission insurance policies
For instance, directors can configure Groups in order that exterior customers aren’t in a position to edit or delete any messages they’ve despatched. Or, an proprietor of a Groups website can disable message enhancing for members of a sure channel.
Preliminary discovery
Whereas I used to be working with the earlier model (v0.4.4) of AADInternals Groups capabilities I observed an attention-grabbing factor: I used to be in a position to edit and delete chat messages utilizing AADInternals as a visitor
even when it was not allowed.
This led to a query that what if the insurance policies are utilized solely on the consumer finish? In observe this is able to imply that the Groups service tells to your Groups consumer that “Although shall not edit messages!” however the consumer
might nonetheless accomplish that.
Observing Groups consumer behaviour
I began by watching what was occurring between the consumer and cloud when the Groups consumer began. The primary statement was that the consumer made about 120 http requests to the cloud.
Whereas looking by means of these requests, I noticed one which caught my curiosity (headers stripped):
POST https://groups.microsoft.com/api/mt/half/emea-02/beta/customers/useraggregatesettings HTTP/1.1
{
"tenantSettingsV2": true,
"userResourcesSettings": true,
"messagingPolicy": true,
"clientSettings": true,
"targetingPolicy": true,
"tenantSiteUrl": true,
"userPropertiesSettings": true,
"callingPolicy": true,
"meetingPolicy": true,
"educationAssignmentsAppPolicy": true
}
The response contained all of the settings and insurance policies the Groups consumer is allowed to do because the logged in consumer. Under could be seen the messagingPolicy part:
"messagingPolicy": {
"worth": {
"allowUserEditMessage": true,
"allowUserDeleteMessage": true,
"allowUserChat": true,
"allowGiphy": true,
"giphyRatingType": "Average",
"allowGiphyDisplay": true,
"allowPasteInternetImage": true,
"allowMemes": true,
"allowStickers": true,
"allowUserTranslation": true,
"allowUrlPreviews": true,
"readReceiptsEnabledType": "UserPreference",
"allowImmersiveReader": true,
"allowPriorityMessages": true,
"audioMessageEnabledType": "ChatsAndChannels",
"channelsInChatListEnabledType": "DisabledUserOverride",
"allowRemoveUser": true,
"allowSmartReply": true
}
}What we will study right here is that the Groups consumer asks from the cloud what the present consumer is allowed to do, which was the anticipated behaviour.
Testing in motion
Subsequent I made a decision to attempt whether or not I might deceive Groups consumer:
-
I saved the response from above for use as a baseline.
-
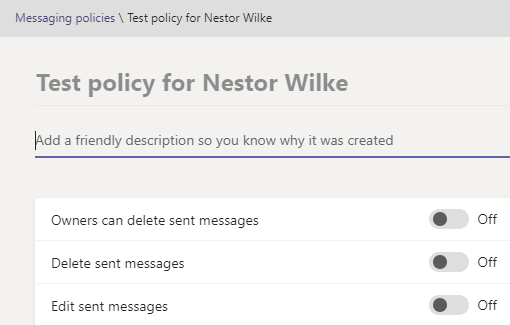
I created a brand new Messaging coverage to disable enhancing and deleting of despatched messages.
I utilized the coverage to a single demo consumer:
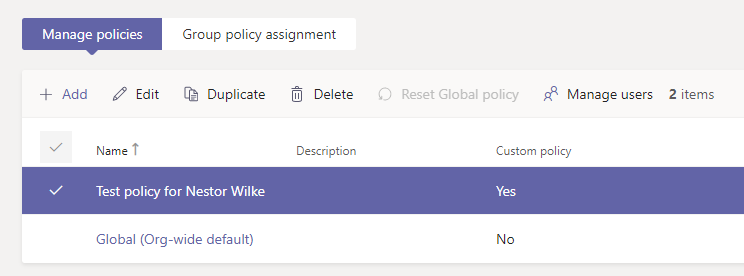
Now I had two insurance policies, the default organisation large and the restricted one for demo consumer:
-
I restarted the Groups consumer and observed that the enhancing and deleting had been accurately disabled (didn’t exists).
-
I in contrast the returned insurance policies from the useraggregatesettings requests
and as we will see, the request was lacking two traces: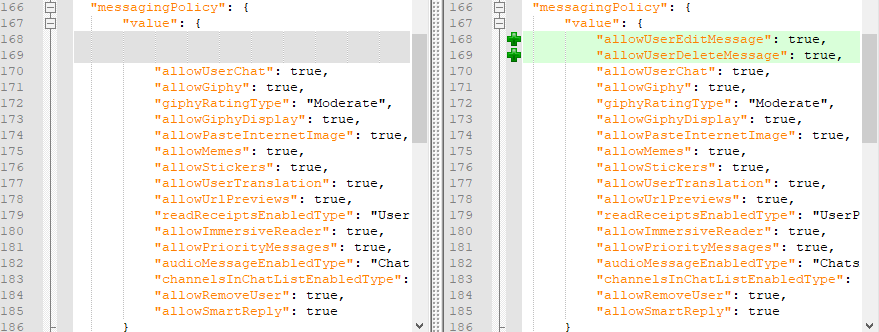
-
I closed the consumer and configured Fiddler to do an autoresponse utilizing the saved http response from above:
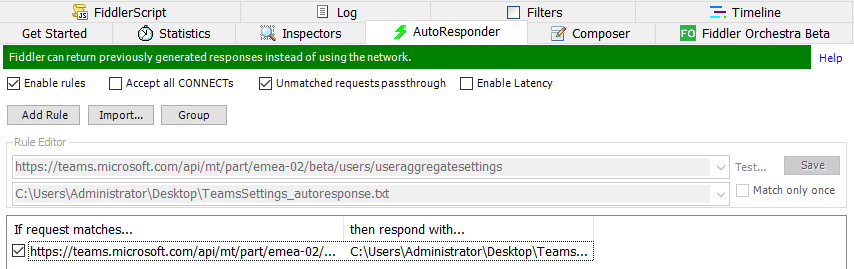
Now, when the consumer is requesting the settings file, it will likely be served the one that enables enhancing and deleting.
-
I began the Groups consumer and the enhancing and deleting had been once more allowed and I used to be in a position to edit and delete (my very own) messages!
What we will lean right here is that we will deceive Groups consumer and alter its behaviour :pleasure:
Furthermore, we learnt that Groups insurance policies are utilized solely on the consumer :man_facepalming:
Right here is the video demonstrating this with AADInternals and Fiddler (sorry for the unhealthy audio after 03:20):
Under is a video that reveals in motion that this works additionally with cloud file storage restrictions:
Observe: Though not seen on the video, I used to be ready so as to add my Google Drive account to Groups so this isn’t only a UI factor.
So far as I do know, the “uncompliant” Groups consumer behaviour cannot be detected.
Similar verdict with defending. Properly, one might attempt to use Conditional Entry (CA) with system possession and compliance restrictions, however that doesn’t cowl all situations.
Our little check right here proves that Groups insurance policies are utilized ONLY on the consumer!.
If the consumer (or visitor) is utilising Groups APIs instantly, utilizing for example AADInternals Groups performance, she or he can bypass the restrictions set by the insurance policies.
Nonetheless, this isn’t a bug or vulnerability as such, however a (very very unhealthy) design selection by Microsoft.
Customers can do at the very least the next:
- Bypass messaging insurance policies
- Bypass cloud file storage restrictions
- Bypass conferences insurance policies
:warning: Groups insurance policies are NOT a safety measure and organisations shouldn’t depend on them! :warning:














+ There are no comments
Add yours