AADInternals toolkit is greatest recognized of its offensive or crimson groups instruments. Its origins, nevertheless, is in administration – particularly for duties not supported by official instruments.
On this weblog, I’ll introduce latest additions to the admin & blue workforce instruments and in addition some outdated goodies!
There are a number of settings out there within the admin portals affecting the safety of your tenant. I’ve chosen the next capabilities that can assist you to guard your tenant and to simply transfer to trendy authentication.
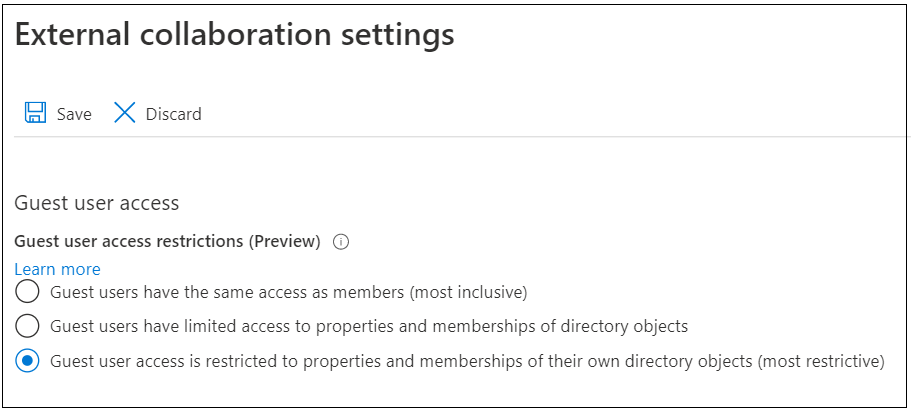
Visitor Entry
As I’ve demonstrated earlier, by default, visitor customers have method an excessive amount of permissions and might successfully export the customers and teams of your tenant.
To guard your tenant from the visitor customers, the Exterior collaboration settings needs to be set to most restrictive:
The standing of this setting can simply be checked with AADInternals:
# Get the entry token
Get-AADIntAccessTokenForMSGraph -SaveToCache
# Get the tenant visitor entry
Get-AADIntTenantGuestAccessOutput:
Entry Description RoleId
------ ----------- ------
Regular Visitor customers have restricted entry to properties and memberships of listing objects 10dae51f-b6af-4016-8d66-8c2a99b929b3
There are three totally different entry ranges:
| Entry stage | Description |
|---|---|
| Inclusive | Visitor customers have the identical entry as members |
| Regular | Visitor customers have restricted entry to properties and memberships of listing objects |
| Restricted | Visitor person entry is restricted to properties and memberships of their very own listing objects (most restrictive) |
To alter the settings utilizing AADInternals (requires World Administrator position):
# Get the entry token
Get-AADIntAccessTokenForMSGraph -SaveToCache
# Get the tenant visitor entry
Set-AADIntTenantGuestAccess -Degree RestrictedOutput:
Entry Description RoleId
------ ----------- ------
Visitor person entry is restricted to properties and memberships of their very own listing objects (most restrictive) 2af84b1e-32c8-42b7-82bc-daa82404023b
Azure AD Graph API entry
Azure AD is appears to constructed with the precept than on-premises AD that successfully offers read-only permissions to the entire content material of Azure AD, together with tenant-level settings.
I’ve earlier mentioned in regards to the methods to limit customers’s entry to Azure AD knowledge.
The each presently used PowerShell modules (MSOnline and AzureAD) are each utilising Azure AD Graph endpoint.
Microsoft introduced in June 2020 that the end-of-support for AAD Graph API will likely be June thirtieth 2022.
Within the meantime, to disable entry to Azure AD Graph utilizing AADInternals:
# Get the entry token
Get-AADIntAccessTokenForMSGraph -SaveToCache
# Disable entry to AAD Graph API
Disable-AADIntTenantMsolAccess
# Test the settings after 10 seconds or so.
Get-AADIntTenantAuthPolicy | Choose block*Output:
blockMsolPowerShell
-------------------
True
Self-service buy merchandise
Self-service buy merchandise are, because the identify suggests, merchandise that tenant customers can buy by themselves. Whereas the merchandise don’t generate any billing for the organisation, they will introduce safety points as they might permit entry to the organisation knowledge.
I just lately learn a terrific article by Tony Redmond (@12Knockssinna) on easy methods to block the self-service purchases per product.
This concerned putting in MS Commerce PowerShell module and enjoying round with product IDs which I felt a bit too difficult.
To dam self-service buy for all merchandise a bit simpler with AADInternals:
# Disable self-service buy for all merchandise
Get-AADIntSelfServicePurchaseProducts | Set-AADIntSelfServicePurchaseProduct -Enabled $falseOutput:
Product Id Standing
------- -- ------
Home windows 365 Enterprise CFQ7TTC0HHS9 Disabled
Home windows 365 Enterprise with Home windows Hybrid Profit CFQ7TTC0HX99 Disabled
Home windows 365 Enterprise CFQ7TTC0J203 Disabled
Energy Automate per person CFQ7TTC0KP0N Disabled
Energy Apps per person CFQ7TTC0KP0P Disabled
Energy Automate RPA CFQ7TTC0KXG6 Disabled
Energy BI Premium (standalone) CFQ7TTC0KXG7 Disabled
Visio Plan 2 CFQ7TTC0KXN8 Disabled
Visio Plan 1 CFQ7TTC0KXN9 Disabled
Mission Plan 3 CFQ7TTC0KXNC Disabled
Mission Plan 1 CFQ7TTC0KXND Disabled
Energy BI Professional CFQ7TTC0L3PB Disabled
Observe: New self-service buy merchandise are launched on common foundation, so don’t overlook to test the merchandise a minimum of as soon as a month!
Unified Audit log
The Unified Audit Log incorporates the next person and admin exercise in Microsoft 365 and Azure AD:
- Consumer exercise in SharePoint On-line and OneDrive for Enterprise
- Consumer exercise in Trade On-line (Trade mailbox audit logging)
- Admin exercise in SharePoint On-line
- Admin exercise in Azure Energetic Listing (the listing service for Microsoft 365)
- Admin exercise in Trade On-line (Trade admin audit logging)
- eDiscovery actions within the safety and compliance middle
- Consumer and admin exercise in Energy BI
- Consumer and admin exercise in Microsoft Groups
- Consumer and admin exercise in Dynamics 365
- Consumer and admin exercise in Yammer
- Consumer and admin exercise in Microsoft Energy Automate
- Consumer and admin exercise in Microsoft Stream
- Analyst and admin exercise in Microsoft Office Analytics
- Consumer and admin exercise in Microsoft Energy Apps
- Consumer and admin exercise in Microsoft Varieties
- Consumer and admin exercise for sensitivity labels for websites that use SharePoint On-line or Microsoft Groups
- Admin exercise in Briefing e-mail and MyAnalytics
As such, the Unified Audit Log is a most important supply or forensic knowledge for any Incident Response (IR) engagement.
You may activate the Unified Audit Log with AADInternals:
# Get the entry token
Get-AADIntAccessTokenForEXO -SaveToCache
# Disable the unified audit log
Set-AADIntUnifiedAuditLogSettings -Enabled trueObserve! It should take hours for the modifications to take impact!
As talked about above, the Unified Audit log incorporates forensic knowledge for Azure AD and Workplace/Microsoft 365. There are additionally different logs containing worthwhile forensic knowledge.
Diagnostic settings
Diagnostic settings are used to configure streaming export of platform logs and metrics for a useful resource to the vacation spot of your selection. You might create as much as 5 totally different diagnostic settings to ship totally different logs and metrics to impartial locations.
Diagnostic settings will be set within the Azure Admin Portal however the performance can also be added to AADInternals.
To view the present settings:
# Get the entry token
$at=Get-AADIntAccessTokenForAzureCoreManagement -SaveToCache
# Record diagnostic settings
Get-AADIntAzureDiagnosticSettingsOutput:
Title : Audit and SignIn to Sentinel
WorkspaceId : /subscriptions/a04293e7-46c8-4bf4-bc6d-1bc1f41afae0/resourcegroups/sentinel/suppliers/microsoft.operationalinsights/workspaces/MySentinel
StorageAccountId :
EventHubAuthorizationRuleId :
EventHubName :
ServiceBusRuleId :
Title : Service Principal to Sentinel
WorkspaceId : /subscriptions/a04293e7-46c8-4bf4-bc6d-1bc1f41afae0/resourcegroups/sentinel/suppliers/microsoft.operationalinsights/workspaces/MySentinel
StorageAccountId :
EventHubAuthorizationRuleId :
EventHubName :
ServiceBusRuleId :
To get particulars of a particular settings:
# Record diagnostic settings for the given workspace
Get-AADAzureIntDiagnosticSettingsDetails -Title "Audit and SignIn to Sentinel"Output:
Log Enabled Retention Enabled Retention Days
--- ------- ----------------- --------------
ProvisioningLogs False False 0
AuditLogs False False 0
SignInLogs False False 0
NonInteractiveUserSignInLogs False False 0
ServicePrincipalSignInLogs False False 0
ManagedIdentitySignInLogs True True 365
To alter the settings:
# Set the diagnostic log settings for the given workspace
Set-AADIntDiagnosticSettingsDetails -Title "Audit and SignIn to Sentinel" -Log ManagedIdentitySignInLogs,AuditLogs,SignInLogs -Enabled $true -RetentionEnabled $true -RetentionDays 365Output:
Log Enabled Retention Enabled Retention Days
--- ------- ----------------- --------------
ProvisioningLogs False False 0
AuditLogs True True 365
SignInLogs True True 365
NonInteractiveUserSignInLogs False False 0
ServicePrincipalSignInLogs False False 0
ManagedIdentitySignInLogs True True 365
Signal-ins log
The sign-ins log is the supply of (nearly) all sign-in occasions.
To get the entries with AADInternals:
# Get the Entry Token and save to cache
Get-AADIntAccessTokenForMSGraph -SaveToCache
# Present the log
Get-AADIntAzureSignInLogOutput:
createdDateTime id ipAddress userPrincipalName appDisplayName
--------------- -- --------- ----------------- --------------
2020-05-25T05:54:28.5131075Z b223590e-8ba1-4d54-be54-03071659f900 199.11.103.31 [email protected] Azure Portal
2020-05-29T07:56:50.2565658Z f6151a97-98cc-444e-a79f-a80b54490b00 139.93.35.110 [email protected] Azure Portal
2020-05-29T08:02:24.8788565Z ad2cfeff-52f2-442a-b8fc-1e951b480b00 11.146.246.254 [email protected] Microsoft Docs
2020-05-29T08:56:48.7857468Z e0f8e629-863f-43f5-a956-a4046a100d00 1.239.249.24 [email protected] Azure Energetic Listing PowerShell
To see the small print of a particular entry:
# Present the data for a single entry
Get-AADIntAzureSignInLog -EntryId b223590e-8ba1-4d54-be54-03071659f900Output:
id : b223590e-8ba1-4d54-be54-03071659f900
createdDateTime : 2020-05-25T05:54:28.5131075Z
userDisplayName : admin firm
userPrincipalName : [email protected]
userId : 289fcdf8-af4e-40eb-a363-0430bc98d4d1
appId : c44b4083-3bb0-49c1-b47d-974e53cbdf3c
appDisplayName : Azure Portal
ipAddress : 199.11.103.31
clientAppUsed : Browser
userAgent : Mozilla/5.0 (Home windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.138 Safari/537.36
...
Audit log
The audit log is the supply of (nearly) all Azure AD associated audit occasions.
To get the audit log with AADInternals:
# Get the Entry Token and save to cache
Get-AADIntAccessTokenForMSGraph -SaveToCache
# Present the log
Get-AADIntAzureAuditLogOutput:
id activityDateTime activityDisplayName operationType consequence initiatedBy
-- ---------------- ------------------- ------------- ------ -----------
Directory_9af6aff3-dc09-4ac1-a1d3-143e80977b3e_EZPWC_41985545 2020-05-29T07:57:51.4037921Z Add service principal Add success @{person=; app=}
Directory_f830a9d4-e746-48dc-944c-eb093364c011_1ZJAE_22273050 2020-05-29T07:57:51.6245497Z Add service principal Add failure @{person=; app=}
Directory_a813bc02-5d7a-4a40-9d37-7d4081d42b42_RKRRS_12877155 2020-06-02T12:49:38.5177891Z Add person Add success @{app=; person=}
To see the small print of a particular entry:
# Present the data for a single entry
Get-AADIntAzureAuditLog -EntryId Directory_9af6aff3-dc09-4ac1-a1d3-143e80977b3e_EZPWC_41985545Output:
id : Directory_9af6aff3-dc09-4ac1-a1d3-143e80977b3e_EZPWC_41985545
class : ApplicationManagement
correlationId : 9af6aff3-dc09-4ac1-a1d3-143e80977b3e
consequence : success
resultReason :
activityDisplayName : Add service principal
activityDateTime : 2020-05-29T07:57:51.4037921Z
loggedByService : Core Listing
operationType : Add
initiatedBy : @{person=; app=}
targetResources : {@{id=66ce0b00-92ee-4851-8495-7c144b77601f; displayName=Azure Credential Configuration Endpoint Service; kind=ServicePrincipal; userPrincipalName=;
groupType=; modifiedProperties=System.Object[]}}
additionalDetails : {}
Azure Listing Exercise Log
I used to be just lately launched an Azure log I wasn’t conscious of; Azure Listing Exercise Log:
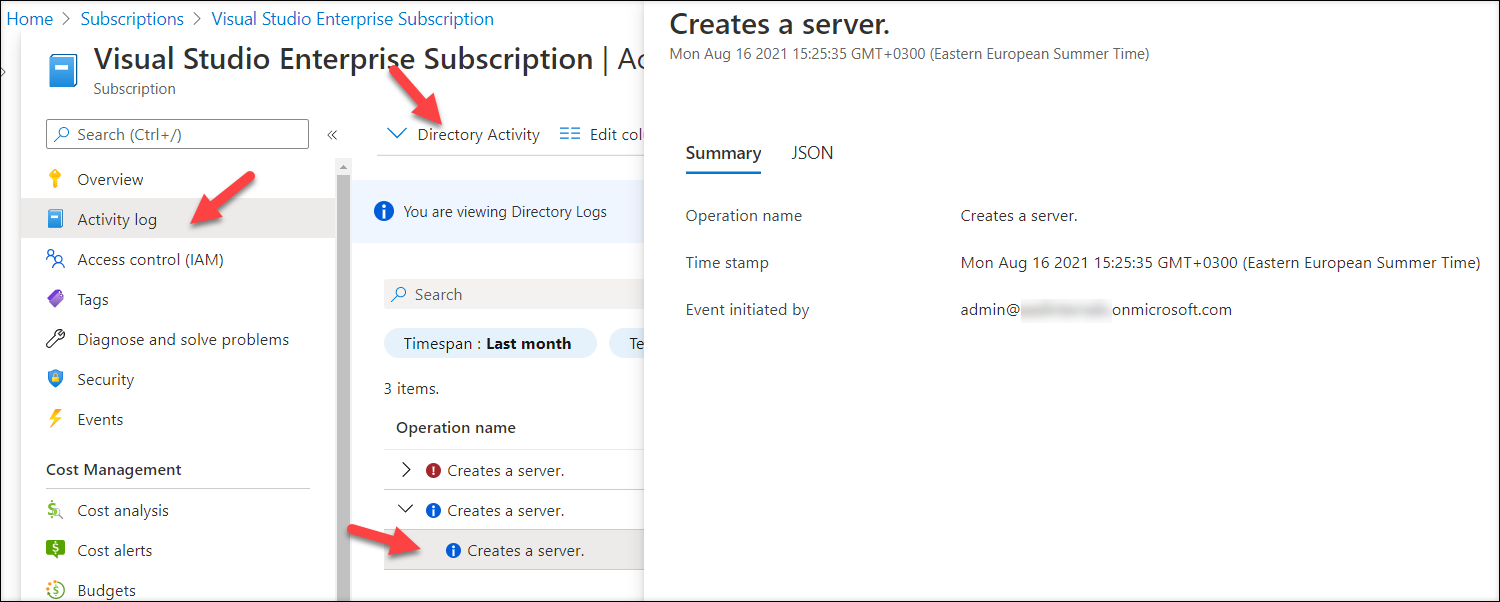
This log incorporates occasions that aren’t out there in different logs. For example, the log has occasions for registering faux AD FS healt brokers and World Directors elevating themselves to Azure admins.
The one caveat is that this log is accessed through Azure subscription, so a minimum of one subscription is required. Because the listing for all subscriptions is identical, additionally the content material of the log is identical for all subscriptions. How about organisations with out an Azure subscriptions?
No worries, the log will be accesses so long as “Entry administration for Azure sources” is switched on:
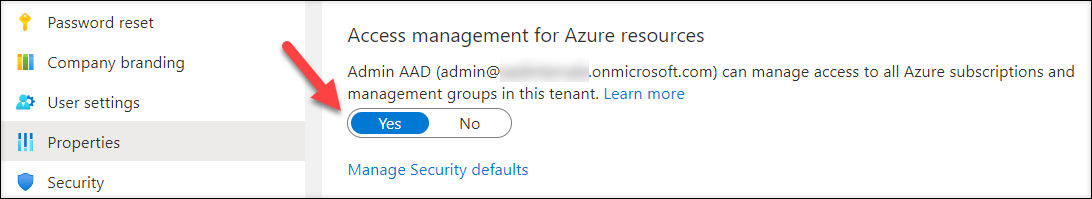
To alter the setting with AADInternals (requires World Administrator position):
# Get the Entry Token
Get-AADIntAccessTokenForAzureCoreManagement -SaveToCache
# Grant Azure Consumer Entry Administrator position
Grant-AADIntAzureUserAccessAdminRoleNow we are able to get the Listing Audit Log occasions (as much as 90 days):
# Get the entry token and save to cache
Get-AADIntAccessTokenForAzureCoreManagement -SaveToCache
# Optionally available: grant Azure Consumer Entry Administrator position
Grant-AADIntAzureUserAccessAdminRole
# Get the occasions for the final month
$occasions = Get-AADIntAzureDirectoryActivityLog -Begin (Get-Date).AddDays(-31)
# Choose ADHybridHealthService associated occasions and extract related info
$occasions | the place {$_.authorization.motion -like "Microsoft.ADHybrid*"} | %{New-Object psobject -Property ([ordered]@{"Scope"=$_.authorization.scope;"Operation"=$_.operationName.localizedValue;"Caller"=$_.caller;"TimeStamp"=$_.eventTimeStamp;"IpAddress"=$_.httpRequest.clientIpAddress})} | ftOutput:
Scope Operation Caller TimeStamp IpAddress
----- --------- ------ --------- ---------
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:10:59.0148112Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:10:58.3348792Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:10:16.2093169Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:10:15.5693784Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:07:11.3219081Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:07:10.5819036Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:04:18.1500781Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts2.firm.com Creates a server. [email protected] 2021-08-25T15:04:17.7750301Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService Updates a service. [email protected] 2021-08-25T15:02:33.2797177Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService Updates a service. [email protected] 2021-08-25T15:02:33.0297112Z 51.65.246.212
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts.firm.com Deletes service. [email protected] 2021-08-25T15:01:26.9612649Z 152.219.25.6
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts.firm.com Deletes service. [email protected] 2021-08-25T15:01:26.7262514Z 152.219.25.6
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts.firm.com Deletes service. [email protected] 2021-08-25T15:01:18.4399245Z 152.219.25.6
/suppliers/Microsoft.ADHybridHealthService/providers/AdFederationService-sts.firm.com Deletes service. [email protected] 2021-08-25T15:01:18.2599207Z 152.219.25.6
/suppliers/Microsoft.ADHybridHealthService Updates a service. [email protected] 2021-08-25T15:00:00.5760736Z 152.219.25.6
/suppliers/Microsoft.ADHybridHealthService Updates a service. [email protected] 2021-08-25T14:59:53.6402357Z 152.219.25.6
Unified Audit log
As talked about earlier, the Unified Audit Log is the primary supply of forensic occasions of Azure AD and Microsoft/Workplace 365. Nevertheless, the present instruments for looking out and exporting the log are sluggish and troublesome to make use of.
Subsequently, I made a decision to implement the search in AADInternals (technicalyy makes use of compliance API).
To go looking the log for the primary 150 entries:
# Get compliance API cookies
$cookies = Get-AADIntComplianceAPICookies
# Dump the primary 150 entries from the final 90 days to json file
Search-AADIntUnifiedAuditLog -Cookies $cookies -Verbose -Begin (get-date).AddDays(-90) | Set-Content material auditlog.jsonTo go looking the log for as much as 50100 entries and dump them to json file:
# Dump the entire log (max 50100) from the final 90 days to csv file
Search-AADIntUnifiedAuditLog -Cookies $cookies -Verbose -Begin (get-date).AddDays(-90) -All | Set-Content material auditlog.jsonTo go looking the log for as much as 50100 entries and dump them to csv file:
# Dump the entire log (max 50100) from the final 90 days to csv file
Search-AADIntUnifiedAuditLog -Cookies $cookies -Verbose -Begin (get-date).AddDays(-90) -All | ConvertTo-Csv | Set-Content material auditlog.csvOpen-Supply Intelligence (OSINT)
OSINT refers back to the info publicly out there, on this case, about tenants and its domains.
Easies method to shortly test the standing of the domains of the tenant with AADInternals is:
# Present the essential info of the tenant and domains
Invoke-AADIntReconAsOutsider -Area firm.com | Format-DeskOutput:
Tenant model: Firm Ltd
Tenant identify: firm
Tenant id: 05aea22e-32f3-4c35-831b-52735704feb3
DesktopSSO enabled: False
Title DNS MX SPF DMARC Kind STS
---- --- -- --- ----- ---- ---
firm.com True True True True Federated sts.firm.com
firm.mail.onmicrosoft.com True True True False Managed
firm.onmicrosoft.com True True True False Managed
int.firm.com False False False False Managed
This helps in troubleshooting as an example mailrouting and spam issues, comparable to, are MX data pointing to the cloud or are SPF & DMARC data configured?












+ There are no comments
Add yours